Navigating the NIST Post-Quantum Cryptography (PQC) Roadmap
The National Institute of Standards and Technology (NIST) has published a clear roadmap for the transition to post-quantum cryptography (PQC), setting firm deadlines for the deprecation and disallowance of legacy algorithms including RSA and Elliptic Curve Cryptography (ECC). These deadlines are not aspirational targets — they represent the point at which current cryptographic standards will cease to be approved for use.
This guide explains what the NIST PQC timeline means for your organisation, which algorithms have been approved, and the practical steps you need to take to prepare. Whether you are in central government, defence, financial services, or enterprise, the clock is running.
What Is Post-Quantum Cryptography (PQC)?
Post-quantum cryptography refers to cryptographic algorithms designed to be secure against attack by both classical and quantum computers. Current public key algorithms — RSA, ECC, and Diffie-Hellman — rely on mathematical problems that quantum computers will be able to solve efficiently. Once sufficiently powerful quantum computers become available, these algorithms will no longer protect data.
PQC algorithms are based on different mathematical foundations — lattice problems, hash functions, and error-correcting codes — that are believed to resist quantum attack. NIST has led a multi-year standardisation process to evaluate and select these algorithms, and the first approved standards were published in 2024.
The quantum threat is not theoretical or distant. The harvest now, decrypt later strategy means that adversaries are already capturing encrypted data today with the intention of decrypting it once quantum capability matures. Data with a long confidentiality requirement — government secrets, intellectual property, health records, financial data — is at risk now, not in 2035. This is a business transformation, not merely an algorithm swap.
The NIST PQC Standardisation Timeline
NIST has set out clear milestones that organisations must plan against. The two critical deadlines are 2030, when RSA and ECC will be deprecated, and 2035, when they will be disallowed entirely. But the transition must begin well before those dates — the NCSC recommends UK organisations start preparing now.
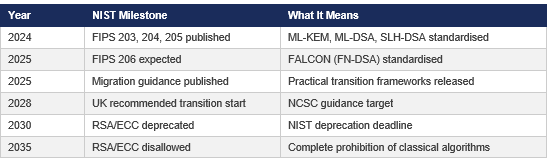
The G7 Cyber Expert Group has endorsed the 2035 target specifically for financial services, reinforcing that this is a global regulatory expectation, not a US-only initiative.
Post-2030, systems using deprecated algorithms may still function but will not align with modern security standards, exposing organisations to compliance risk. Post-2035, these systems may completely fail to interoperate with PQC-ready infrastructure or be outright prohibited by regulators.
NIST PQC Approved Algorithms
NIST’s standardisation process has produced the following approved algorithms. These are the replacements for RSA, ECC, and Diffie-Hellman that your organisation will need to adopt.
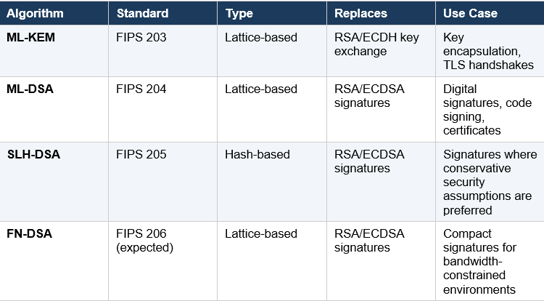
ML-KEM (formerly CRYSTALS-Kyber) handles key exchange — the process by which two parties establish a shared secret over an insecure channel. ML-DSA (formerly CRYSTALS-Dilithium) handles digital signatures — proving the authenticity and integrity of data, certificates, and code. SLH-DSA (formerly SPHINCS+) provides a hash-based alternative for organisations that want signatures based on more conservative, well-understood mathematical assumptions. FN-DSA (formerly FALCON) offers smaller signature sizes, which matters in bandwidth-constrained environments such as IoT and embedded systems.
Your hardware security modules must support these new algorithms. Thales Luna 7 firmware already includes ML-DSA and ML-KEM functionality modules, and Crypto4A QxHSM supports both classical and post-quantum algorithms natively as a crypto-agile platform.
Practical Migration Steps for PQC Readiness
The transition to post-quantum cryptography is a multi-year programme, not a single upgrade event. Organisations that start planning now will avoid the compressed timelines and elevated risk that come with leaving it until 2029. The following steps provide a practical framework for PQC readiness.
Step 1: Build Your Cryptographic Inventory
You cannot migrate what you cannot see. The first step is a comprehensive audit of every cryptographic asset in your environment — certificates, keys, algorithms, protocols, and the systems that depend on them. A typical Windows environment may contain between 80,000 and 500,000 certificates, and most organisations have no centralised record of where legacy algorithms like RSA-2048 or ECDSA P-256 are in use.
Unsung’s Cryptographic Bill of Materials (CBOM) service provides this visibility. We discover cryptographic assets across IT, OT, cloud, and endpoint environments, map them to business services, and classify each by PQC vulnerability. This inventory becomes the foundation for every subsequent migration decision. For practical guidance on getting started, see our blog post on building a cryptographic inventory.
Step 2: Prioritise by Risk
Not all cryptographic assets carry the same risk. Prioritisation should be driven by three factors: the sensitivity and longevity of the data being protected, the exposure of the system to external networks, and the regulatory obligations that apply.
Data with long confidentiality requirements — state secrets, intellectual property, patient records — should be prioritised first because it is already vulnerable to harvest-now-decrypt-later attacks. Internet-facing systems come next, followed by internal systems with lower sensitivity. Classify your inventory into tiers: migrate immediately, migrate by 2028, and migrate by 2030. This avoids the trap of treating every system as equally urgent, which leads to paralysis.
Step 3: Evaluate Vendor PQC Roadmaps
Your migration timeline depends heavily on when your technology vendors deliver PQC support. Audit the PQC roadmaps of every vendor in your cryptographic supply chain — HSM manufacturers, certificate authority platforms, TLS libraries, VPN providers, cloud services, and application frameworks.
Key questions to ask: which NIST-approved algorithms are supported today? What is the timeline for full production support? Are firmware or software updates included in existing support contracts, or will they require additional licensing? Be cautious of vendor claims that need scrutiny — “PQC-ready” means different things to different vendors, and marketing claims should be validated against actual implementation status and independent certification.
Step 4: Plan Hybrid Certificate Deployment
The transition will not be instantaneous. During the migration period, your systems will need to communicate with both PQC-ready and legacy-only endpoints. Hybrid certificates — containing both a classical and a post-quantum algorithm — allow this interoperability. A system that supports PQC will use the quantum-safe algorithm; a legacy system will fall back to the classical one.
Hybrid deployment requires careful planning around certificate profiles, CA configuration, and application compatibility testing. Your PKI architecture needs to support dual-algorithm certificates without breaking existing validation chains or introducing unacceptable performance overhead. This is particularly important for environments with legacy IT systems that need architectural wrappers to bridge the gap.
Step 5: Test with Crypto4A QxEmulator
Before committing to production migration, organisations need a safe environment to test PQC algorithm integration with their existing applications and infrastructure. Crypto4A’s QxEmulator provides exactly this — a software-based emulation of the QxHSM that allows your development and security teams to test post-quantum algorithm operations without procuring physical hardware.
Testing should cover certificate issuance and validation with PQC algorithms, TLS handshake performance with hybrid and pure PQC configurations, application compatibility across your critical systems, and key ceremony procedures using the new algorithms. Identifying integration issues in a test environment is significantly cheaper than discovering them during production migration.
For five practical steps that don’t require major investment, see our companion guide. And be wary of the trust now, forge later threat that extends the quantum risk beyond confidentiality to digital signatures and authentication.
How Unsung Supports PQC Transition
At Unsung, we specialise in Public Key Infrastructure and post-quantum cryptography. Our team works with organisations across government, defence, financial services, and enterprise to plan and execute PQC transitions that are practical, phased, and aligned with business reality.
Audit and Assessment
We conduct comprehensive cryptographic asset audits using our CBOM service, identifying every instance of legacy cryptography across your infrastructure — hardware, firmware, applications, and services. This gives you the visibility to make informed migration decisions.
PQC Strategy Development
We design bespoke PQC transition plans aligned with NIST’s timelines and NCSC guidance, with a focus on crypto agility — ensuring your architecture can adopt new algorithms as they emerge without requiring wholesale infrastructure replacement. Our strategies cover prioritisation, vendor roadmap alignment, hybrid deployment planning, and resource requirements.
Implementation Across Systems
From upgrading hardware security modules to migrating keys and certificates, we handle the technical delivery. Our implementation services cover HSMs, certificate authorities, enterprise networks, embedded systems, and critical infrastructure. We work with your existing technology stack and support integration of ML-DSA, ML-KEM, and other NIST-approved algorithms.
Managed Services for Quantum Security
Post-transition, we provide ongoing support to maintain your quantum-safe posture. We monitor cryptographic security, manage firmware and software updates, and maintain the crypto agility needed to adapt as post-quantum standards continue to mature. Our PKI Management & Hosting services ensure continuous compliance and operational resilience.
Cutting Through PQC Vendor Noise
Transitioning to post-quantum cryptography does not have to be overwhelming. Whilst some vendors create urgency to push unnecessary solutions, a measured and well-informed approach delivers better outcomes. Unsung’s vendor-neutral position means we recommend solutions based on your requirements, not commercial relationships. We have examined why vendor claims need scrutiny and why lessons from previous hype cycles should inform how the industry approaches PQC.
Frequently Asked Questions About Post-Quantum Cryptography
What is post-quantum cryptography?
Post-quantum cryptography (PQC) refers to cryptographic algorithms designed to remain secure against attack by both classical and quantum computers. Current public key algorithms such as RSA and Elliptic Curve Cryptography rely on mathematical problems that quantum computers will be able to solve efficiently. PQC algorithms use different mathematical foundations — lattice problems, hash functions, and error-correcting codes — that are believed to resist quantum attack. NIST has led a multi-year standardisation process and published the first approved PQC standards (FIPS 203, 204, and 205) in 2024.
When will RSA and ECC be deprecated?
NIST has set two firm deadlines. In 2030, RSA and ECC algorithms will be deprecated, meaning systems using them will no longer comply with NIST-approved security standards. In 2035, these algorithms will be disallowed entirely — organisations still reliant on them will face compliance violations, interoperability failures, and potential regulatory action. The NCSC recommends UK organisations begin active transition planning now, with migration underway by 2028.
What is harvest now, decrypt later?
Harvest now, decrypt later (HNDL) is an attack strategy where adversaries capture encrypted data today and store it until quantum computers capable of breaking the encryption become available. This means data encrypted with RSA or ECC that has a long confidentiality requirement — government secrets, intellectual property, health records, financial data — is already at risk, not just when quantum computers arrive. HNDL is the primary reason organisations cannot afford to wait until 2030 to begin their PQC transition.
What are ML-KEM and ML-DSA?
ML-KEM (Module-Lattice-Based Key Encapsulation Mechanism, formerly CRYSTALS-Kyber) is the NIST-approved algorithm for key exchange, standardised as FIPS 203. It replaces RSA and ECDH for establishing shared secrets over insecure channels. ML-DSA (Module-Lattice-Based Digital Signature Algorithm, formerly CRYSTALS-Dilithium) is the NIST-approved algorithm for digital signatures, standardised as FIPS 204. It replaces RSA and ECDSA for signing certificates, code, and documents. Both are lattice-based algorithms and form the core of most PQC migration plans.
What is a hybrid certificate?
A hybrid certificate contains both a classical algorithm (such as RSA or ECC) and a post-quantum algorithm (such as ML-DSA). During the transition period, hybrid certificates allow systems to communicate securely regardless of whether the recipient supports PQC. A PQC-ready system uses the quantum-safe algorithm; a legacy system falls back to the classical one. Hybrid deployment is essential for maintaining interoperability during migration and requires careful planning around certificate profiles, CA configuration, and application compatibility.
Do hardware security modules support post-quantum algorithms?
Yes, leading HSM vendors are actively adding PQC support. Thales Luna 7 firmware includes functionality modules for ML-DSA, ML-KEM, and LMS/HSS hash-based signatures. Crypto4A QxHSM is purpose-built as a crypto-agile platform supporting both classical and post-quantum algorithms natively. Organisations should audit their existing HSM estate to determine whether current hardware can be upgraded via firmware or whether replacement is required — this is a critical dependency in any PQC migration timeline.
What is a cryptographic bill of materials (CBOM)?
A CBOM is a comprehensive inventory of every cryptographic asset in your environment — certificates, keys, algorithms, protocols, and the systems that depend on them. It is the essential first step in PQC readiness because you cannot migrate what you cannot see. A typical enterprise environment contains tens of thousands of certificates across IT, OT, cloud, and endpoint systems, most of which are not centrally tracked. Unsung's CBOM service discovers these assets, maps them to business services, and classifies each by PQC vulnerability to create a prioritised migration plan.
How long does a PQC transition take?
A realistic PQC transition is a multi-year programme. The timeline depends on the size and complexity of your cryptographic estate, vendor readiness, regulatory obligations, and internal resource availability. For a large enterprise or government organisation, expect 18 to 36 months from initial CBOM assessment through to production migration of priority systems. This is precisely why NIST and the NCSC recommend starting now rather than waiting — organisations that begin in 2028 will face compressed timelines, higher costs, and elevated risk of disruption.
Is PQC only relevant to government and defence?
No. While government and defence organisations face the most immediate regulatory pressure, PQC affects every organisation that uses public key cryptography — which is effectively everyone. Financial services institutions are subject to the G7 Cyber Expert Group's 2035 target. Healthcare organisations protecting patient data have long confidentiality requirements that make HNDL a present-day risk. Any organisation using TLS, code signing, digital signatures, or PKI will need to transition. The question is not whether you need to act, but when — and starting earlier gives you more control over costs, timelines, and risk.
Start Your PQC Journey
The clock is running. By starting your PQC transition now, you can ensure compliance with NIST deadlines, safeguard your systems against emerging quantum threats, and build a foundation of digital trust that will endure the post-quantum era. Unsung has the expertise, partnerships, and track record to guide your organisation through this transformation, our PKI consulting team has delivered PQC readiness assessments and migration planning across government, defence, and enterprise environments. Combining deep cryptographic expertise with practical delivery experience to help organisations move confidently from roadmap to execution.


